Revoking a users sessions in Azure AD is a fantastic way to automatically respond to identity alerts like impossible travel or unfamiliar sign in properties, it becomes an even stronger response the greater your MFA coverage is, and the more apps you use Azure AD for authentication. However automating that response for legitimate actions, like where a user is using a VPN or has a new device, can lead you down a cycle where their sessions are revoked, they sign back in, trigger an alert again, have their sessions revoked and so on.
We can use a Logic App and a custom table to put some intelligence behind this and effectively whitelist a user for a given period. You could possibly achieve the same result using a Sentinel watchlist, but it is currently difficult to remove users from watchlists, though I suspect that functionality will come soon. For this example we have called the table RevokedUsers_CL
First, lets choose a Sentinel analytics rule to trigger this on. For this example we will use impossible travel, you can write your queries and do your entity mapping to suit your environment, but a straight forward example is below
SecurityAlert
| where AlertName == 'Impossible travel activity'
| where Status contains "New"
| parse Entities with * 'AadUserId": "' aadid_ '",' *
| extend ep_ = parse_json(ExtendedProperties)
| project aadid_, CompromisedEntityThen we map our Account to AADUserID and Name to aadid_ and CompromisedEntity respectively

Now we can build our Logic App to automatically revoke the sessions for users that are flagged for impossible travel. We create a new app and set the trigger as ‘When Azure Sentinel incident creation rule was triggered’ then we want to get our entities that we mapped earlier, and create a couple of variables for use later.

Then we take the entities from the incident and append them to our variables, because each hit on our analytics rule will trigger a separate alert and incident, these will only ever be a single user.

Now we are going to run a query against our custom table to see if the user exists and has had their sessions revoked recently.
RevokedUsers_CL
| where TimeGenerated > ago(3d)
| where AADUserID_g =~ "@{variables('AADUserID')}"
| extend UserPrincipalName = UserPrincipalName_s
| extend AADUserID = AADUserID_g
| project TimeGenerated, UserPrincipalName, AADUserIDFor this example we will look through at the last 3 days of logs in our custom table, and just tidy the columns up a bit using the extend operator. If the persons Azure AD Object ID appears in that result, we know they have had their session revoked in the last 3 days and will leave them alone, if it comes back empty then we will revoke their sessions. You could make it 24 hours or a week or whatever suits your environment.
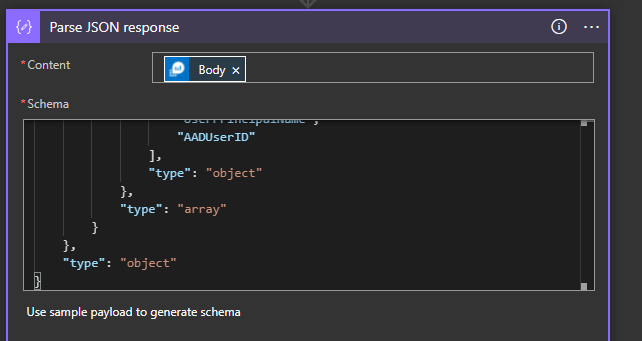
Next we parse the response from Sentinel, because we will need to run a condition over it in the next step
We add a condition to our Logic App to check if the response is empty by checking the length of the result
length(body('Parse_JSON_response')?['value'])
If it equals 0 then the user hasn’t had their sessions revoked in the last 3 days (because they weren’t found in our query) so we will perform the true action, if there is a response then we perform the false action.

So for true, we get their details from Azure AD, refresh their tokens (using an account with sufficient permissions), then we compose a small JSON payload to send back into our custom table to keep it up to date and send it using the Log Analytics Data Collector. We can also send the user an email saying ‘Hi, we noticed strange activity so we have logged you out’ and add a comment to the Sentinel incident, those steps are obviously optional. If the result is false and they have already been logged out in the last 3 days (because our query returned data), we just add a comment to our incident saying ‘this user has already been logged out recently’.
The last step is to create an automation rule that will run this Logic App for us automatically when an incident is created. Edit the analytics rule and selected the automated response option.
Add a new incident automation

Give your automation rule a name and then select the Logic App you just created

Now when your analytics rule fires, they will be automatically logged out of Azure AD and their details put into your rolling whitelist.

2 thoughts on “Using Sentinel to automatically respond to identity alerts”
2 Pingback