Azure Key Vault is Microsoft’s cloud vault which you can use to store secrets and passwords, API keys or certificates. If you do any kind of automation with Azure Functions, or Logic Apps or any scripting more broadly in Azure then there is a good chance you use a Key Vault, its authentication and role based access is tied directly into Azure Active Directory. When we talk about Azure Key Vault security, we can group it into three categories –
- Network Security – this is pretty straight forward, which networks can access your Key Vault.
- Management Plane Security – the management plane is where you manage the Key Vault itself, so changing settings, or generating secrets, or updating access policies. Management plane security is controlled by Azure RBAC.
- Data Plane Security – data plane security is the security of the data within the Key Vault, so accessing, editing or deleting secrets, keys and certificates.
Firstly, make sure you are sending diagnostic logs to Azure Sentinel which you can do on the ‘Diagnostics setting’ tab on a Key Vault, or more uniformly across all your Key Vaults through Azure Policy or Azure Security Center. Events get sent to the AzureDiagnostics table in Azure Sentinel. This table can be tricky to make your way around – because so many various Azure services send logs to it, each with varying data structures, you will notice a lot of columns will only exist for specific actions.
Let’s first look at network security, Key Vault networking isn’t too difficult to get a handle on thankfully. A Key Vault can be accessed either from anywhere on the internet or from a list of specifically allowed IP addresses and/or private endpoints. If your security stance is that Key Vaults are only to be accessed over an allowed list of IP addresses or private endpoints then you can detect when the policy is changed to allow all by default.
// Detects when an Azure Key Vault firewall is set to allow all by default
AzureDiagnostics
| where ResourceType == "VAULTS"
| where OperationName == "VaultPatch"
| where ResultType == "Success"
| project-rename ExistingACL=properties_networkAcls_defaultAction_s, VaultName=Resource
| where isnotempty(ExistingACL)
| where ExistingACL == "Deny"
| sort by TimeGenerated desc
| project
TimeGenerated,
SubscriptionId,
VaultName,
ExistingACL
| join kind=inner
(
AzureDiagnostics
| project-rename NewACL=properties_networkAcls_defaultAction_s, VaultName=Resource
| where ResourceType == "VAULTS"
| where OperationName == "VaultPatch"
| where ResultType == "Success"
| summarize arg_max(TimeGenerated, *) by VaultName, NewACL
)
on VaultName
| where ExistingACL != NewACL and NewACL == "Allow"
| project DetectionTime=TimeGenerated1, VaultName, ExistingACL, NewACL, SubscriptionId, IPAddressofActor=CallerIPAddress, Actor=identity_claim_http_schemas_xmlsoap_org_ws_2005_05_identity_claims_upn_s
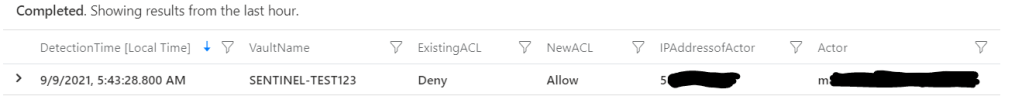
We can see the ACL on the Key Vault firewall has flipped from Deny to Allow. Just a note about the AzureDiagnostics table, if the current ACL is set to ‘Deny’ and you complete other actions (maybe adding a secret, or changing some other settings) on the Key Vault, then that field will keep showing as ‘Deny’ on every action and every log, it doesn’t appear only when making changes to the firewall. So when we join the table in our query we look for when the ACL column has changed and the most recent record (using arg_max) is ‘Allow’.
If you have an approved group of IP ranges you allow, such as your corporate locations, you can also detect for ranges added over and above that in a similar way. This could be an adversary trying to maintain access to a Key Vault they have accessed, or a staff member circumventing policy.
// Detects when an IP address has been added to an Azure Key Vault firewall allow list
AzureDiagnostics
| where ResourceType == "VAULTS"
| where OperationName == "VaultPatch"
| where ResultType == "Success"
| where isnotempty(addedIpRule_Value_s)
| project
TimeGenerated,
VaultName=Resource,
SubscriptionId,
IPAddressofActor=CallerIPAddress,
Actor=identity_claim_http_schemas_xmlsoap_org_ws_2005_05_identity_claims_upn_s,
IPRangeAdded=addedIpRule_Value_s
With this detection, we aren’t changing a global firewall rule i.e. from Deny to Allow, but instead adding new ranges to an existing allow list, so we can return the new IP range that was added in our query.
For management plane security; general access to your Key Vault is going to controlled more broadly by Azure RBAC, so anyone with sufficient privilege in management groups, subscriptions, resource groups or on the Key Vault itself will be able to read or change settings – how that is controlled will be completely unique to your environment. A valuable detection in Sentinel is finding any changes to Azure Key Vault access policies however. An access policy defines what operations service principals (users, app registrations or groups) can perform on secrets, keys or certificates stored in your Key Vault. For instance you may have one set of users who can read and list secrets, but not update them, while others have additional access. The following query finds additions to those access policies.
// Detects when a service principal (user, group or app) has been granted access to Key Vault data
AzureDiagnostics
| where ResourceType == "VAULTS"
| where OperationName == "VaultPatch"
| where ResultType == "Success"
| project-rename ServicePrincipalAdded=addedAccessPolicy_ObjectId_g, Actor=identity_claim_http_schemas_xmlsoap_org_ws_2005_05_identity_claims_name_s, AddedKeyPolicy = addedAccessPolicy_Permissions_keys_s, AddedSecretPolicy = addedAccessPolicy_Permissions_secrets_s,AddedCertPolicy = addedAccessPolicy_Permissions_certificates_s
| where isnotempty(AddedKeyPolicy)
or isnotempty(AddedSecretPolicy)
or isnotempty(AddedCertPolicy)
| project
TimeGenerated,
KeyVaultName=Resource,
ServicePrincipalAdded,
Actor,
IPAddressofActor=CallerIPAddress,
AddedSecretPolicy,
AddedKeyPolicy,
AddedCertPolicyWe can also use some more advanced hunting techniques and detect when access was added then removed within a brief period, this may be a sign of an adversary accessing a Key Vault, retrieving the information and then covering their tracks. This is example shows when access was added then removed from a Key Vault within 10 minutes and returns the access changes.
AzureDiagnostics
| where ResourceType == "VAULTS"
| where OperationName == "VaultPatch"
| where ResultType == "Success"
| extend UserObjectAdded = addedAccessPolicy_ObjectId_g
| extend AddedActor = identity_claim_http_schemas_xmlsoap_org_ws_2005_05_identity_claims_upn_s
| extend KeyAccessAdded = tostring(addedAccessPolicy_Permissions_keys_s)
| extend SecretAccessAdded = tostring(addedAccessPolicy_Permissions_secrets_s)
| extend CertAccessAdded = tostring(addedAccessPolicy_Permissions_certificates_s)
| where isnotempty(UserObjectAdded)
| project
AccessAddedTime=TimeGenerated,
ResourceType,
OperationName,
ResultType,
KeyVaultName=Resource,
AddedActor,
UserObjectAdded,
KeyAccessAdded,
SecretAccessAdded,
CertAccessAdded
| join kind=inner
(
AzureDiagnostics
| where ResourceType == "VAULTS"
| where OperationName == "VaultPatch"
| where ResultType == "Success"
| extend RemovedActor = identity_claim_http_schemas_xmlsoap_org_ws_2005_05_identity_claims_upn_s
| extend UserObjectRemoved = removedAccessPolicy_ObjectId_g
| extend KeyAccessRemoved = tostring(removedAccessPolicy_Permissions_keys_s)
| extend SecretAccessRemoved = tostring(removedAccessPolicy_Permissions_secrets_s)
| extend CertAccessRemoved = tostring(removedAccessPolicy_Permissions_certificates_s)
| where isnotempty(UserObjectRemoved)
| project
AccessRemovedTime=TimeGenerated,
ResourceType,
OperationName,
ResultType,
KeyVaultName=Resource,
RemovedActor,
UserObjectRemoved,
KeyAccessRemoved,
SecretAccessRemoved,
CertAccessRemoved
)
on KeyVaultName
| extend TimeDelta = abs(AccessAddedTime - AccessRemovedTime)
| where TimeDelta < 10m
| project
KeyVaultName,
AccessAddedTime,
AddedActor,
UserObjectAdded,
KeyAccessAdded,
SecretAccessAdded,
CertAccessAdded,
AccessRemovedTime,
RemovedActor,
UserObjectRemoved,
KeyAccessRemoved,
SecretAccessRemoved,
CertAccessRemoved,
TimeDeltaSo we have covered network access and management plane access and now we can have a look at possible threats in data plane actions. Each time an action occurs against a key, secret or certificate it is logged to the same AzureDiagnostics table. The most common action will be a retrieval of a current item, but deletions or purges or updates are all logged as well. Over time we can build up a baseline of what is normal access for a Key Vault looks like and then alert for actions outside of that. The below query looks back over 30 days, then compares that to the last day and detects for any new users accessing a Key Vault. Then it also retrieves all the actions taken by that user in the last day.
//Searches for access by users who have not previously accessed an Azure Key Vault in the last 30 days and returns all actions by those users
let operationlist = dynamic(["SecretGet", "KeyGet", "VaultGet"]);
let starttime = 30d;
let endtime = 1d;
let detection=
AzureDiagnostics
| where TimeGenerated between (ago(starttime) .. ago(endtime))
| where ResourceType == "VAULTS"
| where ResultType == "Success"
| where OperationName in (operationlist)
| where isnotempty(identity_claim_http_schemas_xmlsoap_org_ws_2005_05_identity_claims_upn_s)
| project-rename KeyVaultName=Resource, UserPrincipalName=identity_claim_appid_g
| distinct KeyVaultName, UserPrincipalName
| join kind=rightanti (
AzureDiagnostics
| where TimeGenerated > ago(endtime)
| where ResourceType == "VAULTS"
| where ResultType == "Success"
| where OperationName in (operationlist)
| where isnotempty(identity_claim_http_schemas_xmlsoap_org_ws_2005_05_identity_claims_upn_s)
| project-rename
KeyVaultName=Resource,
UserPrincipalName=identity_claim_http_schemas_xmlsoap_org_ws_2005_05_identity_claims_upn_s
| distinct KeyVaultName, UserPrincipalName)
on KeyVaultName, UserPrincipalName;
AzureDiagnostics
| where TimeGenerated > ago(endtime)
| where ResourceType == "VAULTS"
| where ResultType == "Success"
| project-rename
KeyVaultName=Resource,
UserPrincipalName=identity_claim_http_schemas_xmlsoap_org_ws_2005_05_identity_claims_upn_s
| join kind=inner detection on KeyVaultName, UserPrincipalName
| project
TimeGenerated,
UserPrincipalName,
ResourceGroup,
SubscriptionId,
KeyVaultName,
KeyVaultTarget=id_s,
OperationNameWe can also do the same for applications instead of users.
//Searches for access by applications that have not previously accessed an Azure Key Vault in the last 30 days and returns all actions by those applications
let operationlist = dynamic(["SecretGet", "KeyGet", "VaultGet"]);
let starttime = 30d;
let endtime = 1d;
let detection=
AzureDiagnostics
| where TimeGenerated between (ago(starttime) .. ago(endtime))
| where ResourceType == "VAULTS"
| where ResultType == "Success"
| where OperationName in (operationlist)
| where isnotempty(identity_claim_appid_g)
| project-rename KeyVaultName=Resource, AppId=identity_claim_appid_g
| distinct KeyVaultName, AppId
| join kind=rightanti (
AzureDiagnostics
| where TimeGenerated > ago(endtime)
| where ResourceType == "VAULTS"
| where ResultType == "Success"
| where OperationName in (operationlist)
| where isnotempty(identity_claim_appid_g)
| project-rename
KeyVaultName=Resource,
AppId=identity_claim_appid_g
| distinct KeyVaultName, AppId)
on KeyVaultName, AppId;
AzureDiagnostics
| where TimeGenerated > ago(endtime)
| where ResourceType == "VAULTS"
| where ResultType == "Success"
| project-rename
KeyVaultName=Resource,
AppId=identity_claim_appid_g
| join kind=inner detection on KeyVaultName, AppId
| project
TimeGenerated,
AppId,
ResourceGroup,
SubscriptionId,
KeyVaultName,
KeyVaultTarget=id_s,
OperationNameThen finally we can also detect on operations that may be considered malicious or destructive, such as deletions, backups or purges. I have added some example operations, but there is a great list here that may have actions that are more specific to your Key Vaults.
// Detects Key Vault operations that could be malicious
let operationlist = dynamic(
["VaultDelete", "KeyDelete", "SecretDelete", "SecretPurge", "KeyPurge", "SecretBackup", "KeyBackup", "SecretListDeleted", "CertificateDelete", "CertificatePurge"]);
AzureDiagnostics
| where ResourceType == "VAULTS" and ResultType == "Success"
| where OperationName in (operationlist)
| project TimeGenerated,
ResourceGroup,
SubscriptionId,
KeyVaultName=Resource,
KeyVaultTarget=id_s,
Actor=identity_claim_upn_s,
IPAddressofActor=CallerIPAddress,
OperationNameThere are some more queries located on the Sentinel GitHub page and the queries from this post can be found here.
